Why Zero-Knowledge Architecture Is the Future of Financial Communications
Zero-knowledge cryptography has been a topic in academic cryptography for decades. It's becoming a practical technology for enterprise communications — and for regulated financial firms, it represents a meaningful advance over the current architecture of most "secure" communications platforms.
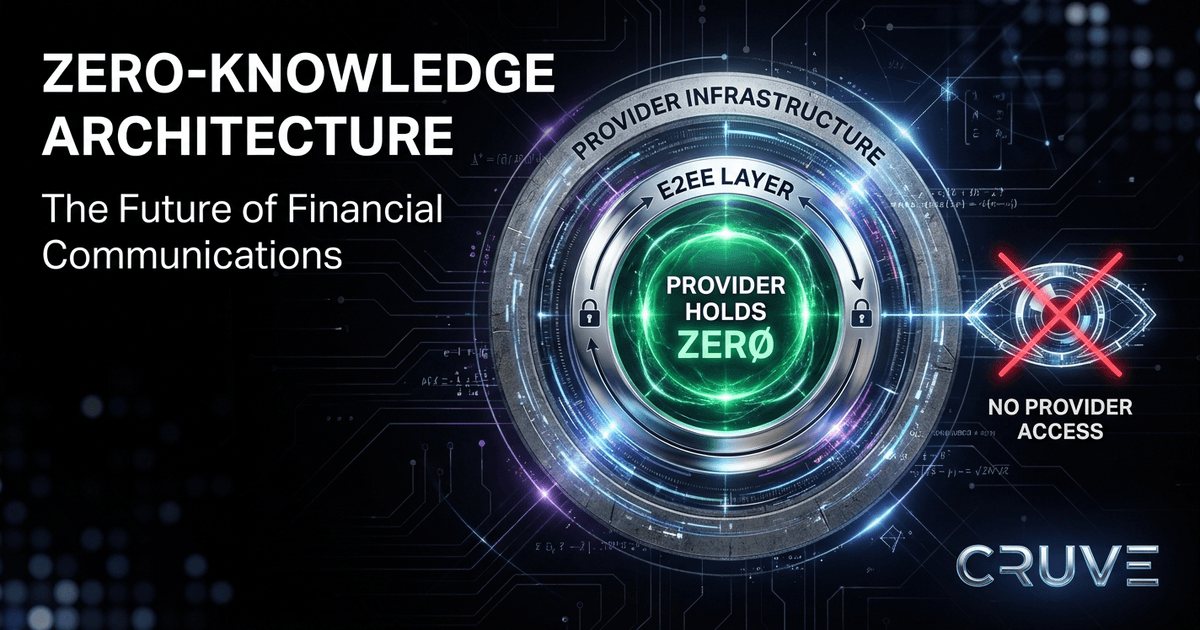
What Zero-Knowledge Actually Means
Zero-knowledge, in the context of cryptography, has a specific technical meaning: a system is zero-knowledge with respect to the communications provider if the provider holds no information about message content that could allow them to read or reconstruct that content, even with full access to their own infrastructure.
This is stronger than conventional end-to-end encryption. In a conventional E2EE system, the provider holds encrypted ciphertext — data that can't be read without the encryption keys, but which represents the message content. If the encryption is ever broken through mathematical advances, implementation flaws, or key exposure, the stored ciphertext becomes readable.
In a zero-knowledge architecture, the provider holds no data that could be used to reconstruct message content, even hypothetically.
The Current Architecture of "Secure" Messaging
Most messaging platforms marketed as "secure" for enterprise use employ one of two approaches:
Encryption in transit (TLS): Messages are encrypted between the user's device and the provider's servers, but the provider decrypts and re-encrypts at each hop. The provider can read message content on their servers.
Conventional E2EE with server-side storage: Messages are end-to-end encrypted between users, and the provider stores encrypted ciphertext. The provider cannot currently read the content, but they store data that could be decrypted if the encryption is ever broken.
Both models have the same fundamental property: the provider holds data on their infrastructure that represents message content. In both cases, a breach of the provider's infrastructure exposes this data to adversaries.
Why This Matters for Financial Communications
Financial communications contain information that is both highly valuable to adversaries and highly sensitive from a regulatory perspective. Client communications contain personal financial information subject to Regulation S-P. Transactional communications may contain material non-public information (MNPI) about pending deals and corporate events. Internal communications contain strategic information and regulatory correspondence.
A breach of a communications provider that holds this information — even in encrypted form — creates significant risk. If the encryption is later broken, historical communications become exposed. For time-sensitive sensitive information, delayed exposure is still exposure.
Zero-Knowledge Architecture in Practice
Implementing zero-knowledge architecture requires the provider to perform necessary operations — message routing, delivery confirmation, notification — without access to message content. The mechanisms that make this possible:
Client-side encryption with provider-blind delivery: Messages are encrypted on the sender's device before transmission. The provider receives encrypted packets with routing metadata but no content. The provider delivers the encrypted packet to the recipient without ever decrypting it.
Sealed sender: The sender's identity is encrypted for the recipient but not accessible to the provider. The provider can deliver the message without knowing who sent it.
Compliance archiving without content exposure: The compliance archive receives content encrypted for the firm's compliance key pair — not Cruve's. Cruve cannot decrypt the archive. The firm can, using their own keys, satisfying the regulatory requirement without provider content access.
The Threat Model That Makes Zero-Knowledge Important
Zero-knowledge architecture is particularly valuable against threat models that conventional E2EE doesn't fully address:
Retroactive decryption: An adversary who records encrypted traffic today and waits for cryptographic advances or key exposure to decrypt it in the future. Zero-knowledge prevents this attack by never exposing encrypted content to provider infrastructure.
Insider threats with extraordinary access: A provider employee with root access could, in a conventional E2EE system, access all archived ciphertext. If the encryption is ever broken, this employee has access to historical communications. Zero-knowledge prevents this by ensuring no ciphertext reaches provider-controlled infrastructure.
Legal process directed at the provider: Subpoenas directed at the provider can compel disclosure of provider-held data. If the provider holds nothing, there is nothing to disclose.
Why Zero-Knowledge Is the Direction the Market Is Moving
Regulatory expectations around data minimization are increasing. The principle that organizations should hold only data they need for legitimate purposes — and no more — is being codified in privacy regulations globally. Applied to communications providers, this principle argues for architectures that don't accumulate provider-held records of client communications.
The threat environment is escalating. Nation-state adversaries and sophisticated criminal organizations have demonstrated the ability to breach major technology companies' infrastructure and maintain persistent access for extended periods. Platforms that hold sensitive financial communications in plaintext or weakly-encrypted form are high-value targets.
Enterprise clients are becoming more sophisticated about security architecture. Procurement and security teams at large financial institutions are asking more specific questions: what data do you hold about our communications, and in what form? The answer that will increasingly satisfy those questions is: we hold nothing. Zero-knowledge architecture.
Firms that build their communications infrastructure on zero-knowledge principles now will have a security posture that holds up as the threat environment continues to evolve.
READY TO BUILD A COMPLIANT COMMUNICATIONS PROGRAM?
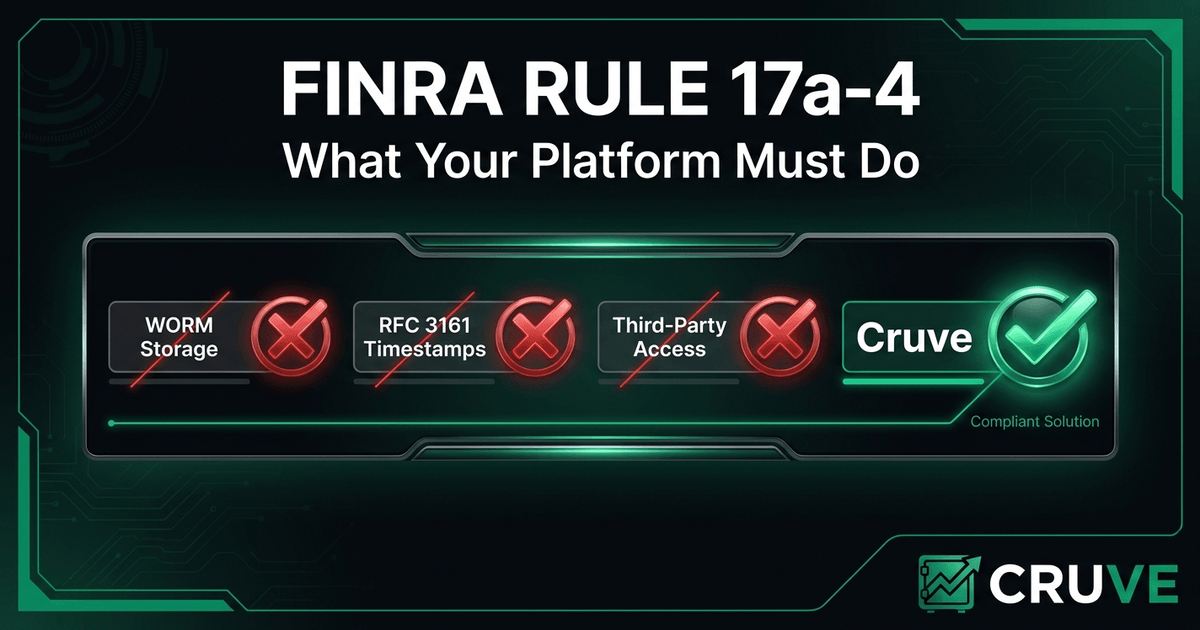
Cruve is purpose-built for FINRA and SEC-regulated firms — E2EE, WORM archiving, and supervisory review in one platform.
Request Early Access