What Is End-to-End Encryption — And Why Your Compliance Officer Should Care
End-to-end encryption is a term that gets used frequently in both consumer privacy discussions and enterprise security conversations, often without much precision about what it actually means or what it doesn't provide. For compliance officers at regulated financial firms, the distinction matters enormously.
What E2EE Actually Means
End-to-end encryption means that a message is encrypted on the sender's device and can only be decrypted by the intended recipient's device. At no point between sender and recipient — not on the provider's servers, not in transit, not in any intermediate storage — can the message be read by anyone other than the intended parties.
The "end" in "end-to-end" refers to the endpoints: the devices where the communication originates and terminates. Traditional encryption — encryption in transit, or TLS — protects data as it moves between points, but the communication provider can decrypt and read the message on their servers. E2EE removes that capability entirely.
The Signal Protocol and Modern E2EE
The Signal Protocol is the gold standard for end-to-end encrypted messaging. Used by Signal, WhatsApp, and Cruve for one-to-one communications, it achieves its security through:
- X3DH (Extended Triple Diffie-Hellman): Key agreement that establishes a shared secret without transmitting private keys
- Double Ratchet Algorithm: Generates a new encryption key for each message, providing forward secrecy and break-in recovery
- 256-bit AES encryption: Symmetric encryption with keys derived from the ratchet algorithm
The result is a system where each individual message is encrypted with a unique key, past keys can't be used to decrypt future messages, and future keys can't be used to decrypt past messages.
MLS for Group Communications
For group communications — what Cruve calls "Lines" — the Signal Protocol's approach to key management doesn't scale efficiently. Messaging Layer Security (MLS), standardized in RFC 9420, is the emerging standard for group E2EE. It provides the same confidentiality guarantees with efficient key management that scales to groups of hundreds of participants.
The Compliance Paradox: E2EE vs. Archiving
Here's where compliance officers typically encounter their first objection to E2EE: if messages can't be read by the provider, how can they be archived for regulatory compliance?
This is a genuine tension, and it's the reason most "enterprise" messaging platforms don't offer true E2EE. They reason that regulatory archiving requirements are incompatible with E2EE, so they don't offer E2EE. The reasoning is wrong. The incompatibility is not inherent — it's an engineering choice.
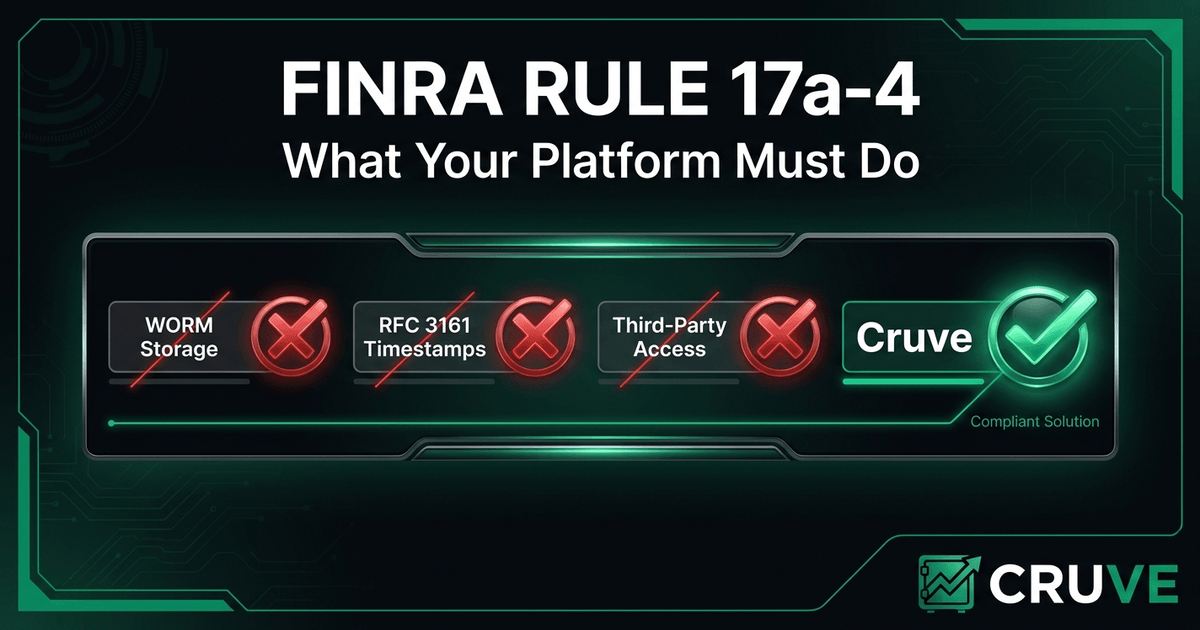
Compliance participant model: The firm's compliance system is treated as an additional participant in every communication. The communication is encrypted for each human recipient AND for a compliance key pair that the firm controls. Messages can be read by intended recipients and by the firm's compliance system — but not by the communication provider, and not by anyone who breaches the provider's infrastructure.
Cruve uses the compliance participant model. Your communications are encrypted for recipients and for your firm's compliance key pair — a key pair that your firm generates and controls, not Cruve. Cruve cannot read your messages. But your firm's compliance officers can decrypt and review communications for supervisory and archiving purposes.
What E2EE Protects Against
E2EE protects against:
- Infrastructure breaches — attackers who breach provider servers get encrypted data they can't read
- Insider threats at the provider — provider employees cannot read your messages
- Legal subpoenas directed at the provider — the provider has no plaintext to give
E2EE does not protect against compromise of endpoint devices, screenshots and manual copying, or legal process directed at the firm's own compliance archive.
Why Compliance Officers Should Advocate for E2EE
The compliance argument for E2EE is often framed as a tension. The better framing is: we need to protect our communications and archive them, so we need E2EE with compliant archiving.
The threat model for financial communications is significant. Your clients share sensitive financial information. Your advisors discuss investment strategies and confidential client data. Your firm handles material non-public information. A breach of your communications provider's infrastructure that exposes this information — because the provider holds plaintext — is a serious problem that E2EE prevents.
The regulatory infrastructure required by Rule 17a-4 can be built in a way that's compatible with E2EE. When it is, you get both: the regulatory compliance your firm requires and the data protection your clients deserve.
READY TO BUILD A COMPLIANT COMMUNICATIONS PROGRAM?
Cruve is purpose-built for FINRA and SEC-regulated firms — E2EE, WORM archiving, and supervisory review in one platform.
Request Early Access