How The Ledger Works: WORM Archiving Explained for Financial Firms
WORM archiving is a regulatory requirement that most compliance officers can cite but fewer can explain in technical detail. That gap matters, because FINRA examiners can — and increasingly do — probe the technical architecture of firms' archiving systems, not just their existence.
What WORM Means, Precisely
WORM stands for Write Once, Read Many. It describes a storage system in which data, once written, cannot be modified or deleted until a specified retention period expires. The "write once" requirement is absolute, not aspirational.
A storage system that has a "do not delete" policy enforced by application controls is not WORM. An administrator with sufficient privileges can change that policy. True WORM storage implements the write-once guarantee at a level below the application — at the storage infrastructure level, in a way that software cannot override.
AWS S3 Object Lock in COMPLIANCE mode is a commonly used implementation. In COMPLIANCE mode, even the AWS account root user cannot delete or modify locked objects before the retention period expires. The guarantee is enforced by AWS's infrastructure, not by any application's policy enforcement.
How The Ledger Implements WORM Storage
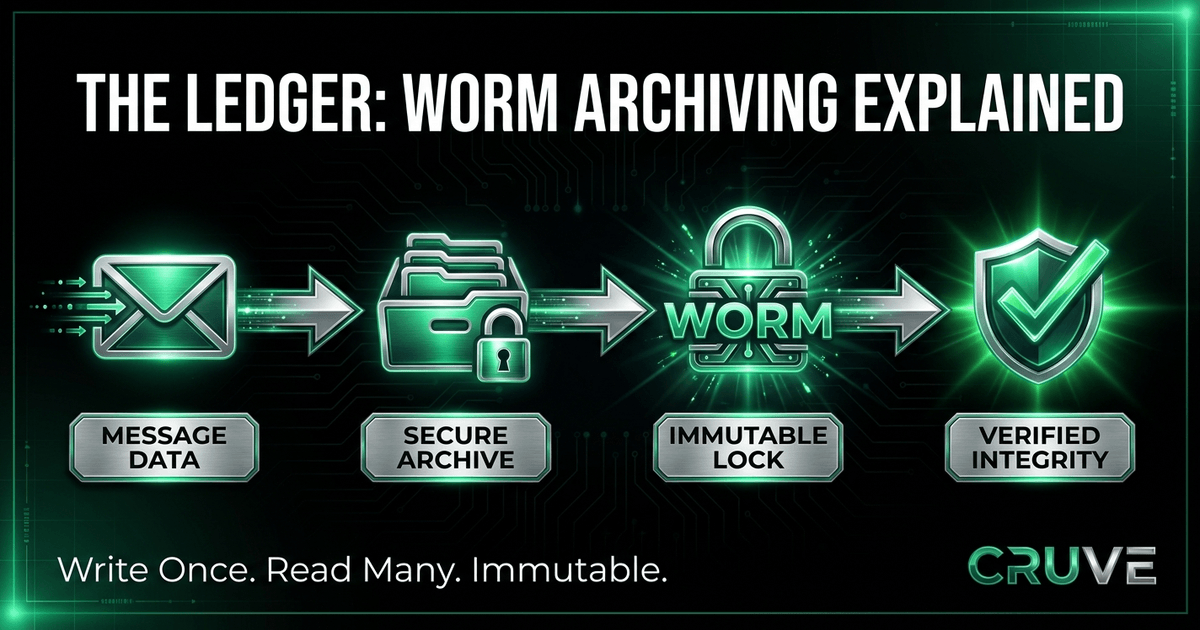
The Ledger — Cruve's compliance archiving system — implements WORM archiving on AWS S3 Object Lock in COMPLIANCE mode. When a message is sent through Cruve:
Step 1: Message creation and archiving occur simultaneously. The archive record is not created through a periodic export or batch process. At the moment a message is sent, the archiving process begins. Message content (encrypted for the compliance key pair), metadata, and associated data (file attachments, reactions, edits, deletions) are written to the archive as an atomic operation.
Step 2: RFC 3161 timestamp is applied. Each archive record is submitted to a trusted timestamp authority that applies an RFC 3161 cryptographic timestamp. This timestamp, signed by a trusted third party, proves the time at which the record was created in a way that cannot be retroactively modified.
Step 3: Record is written to S3 Object Lock storage. The timestamped archive record is written to S3 with Object Lock in COMPLIANCE mode and the retention period set to three years minimum. From this point, the record cannot be modified or deleted until the retention period expires, regardless of any administrative action.
Step 4: Third-party access is maintained. An independent third-party vendor, designated in writing, has independent access to download a complete copy of the archive — satisfying the Rule 17a-4 third-party download requirement.
The Difference Between Archiving and Backup
WORM archiving is frequently confused with backup, but they serve different purposes and have different characteristics.
Backup is designed for recovery: if data is lost or corrupted, backup allows restoration to a previous state. Backup systems typically allow overwrites, have short retention periods, and optimize for recovery speed over evidentiary integrity.
WORM archiving is designed for preservation: records are kept in their original form for the duration of the required retention period, with cryptographic verification that they haven't been modified. Archive systems optimize for integrity and accessibility over recovery speed.
Using a backup system to satisfy Rule 17a-4 archiving requirements is a common compliance mistake that examiners have learned to identify.
The Index and Searchability Requirement
Rule 17a-4 requires not just that records be preserved but that they be indexed and searchable. The Ledger maintains a searchable index of all archived records, indexed by sender and recipient identities, timestamp (with cryptographic verification), message type, communication channel, and keyword content.
This allows compliance officers and regulators to retrieve specific communications — all messages between a particular representative and client, all messages mentioning a specific security, all communications from a date range — without searching through the entire archive.
What Examiners Actually Look For
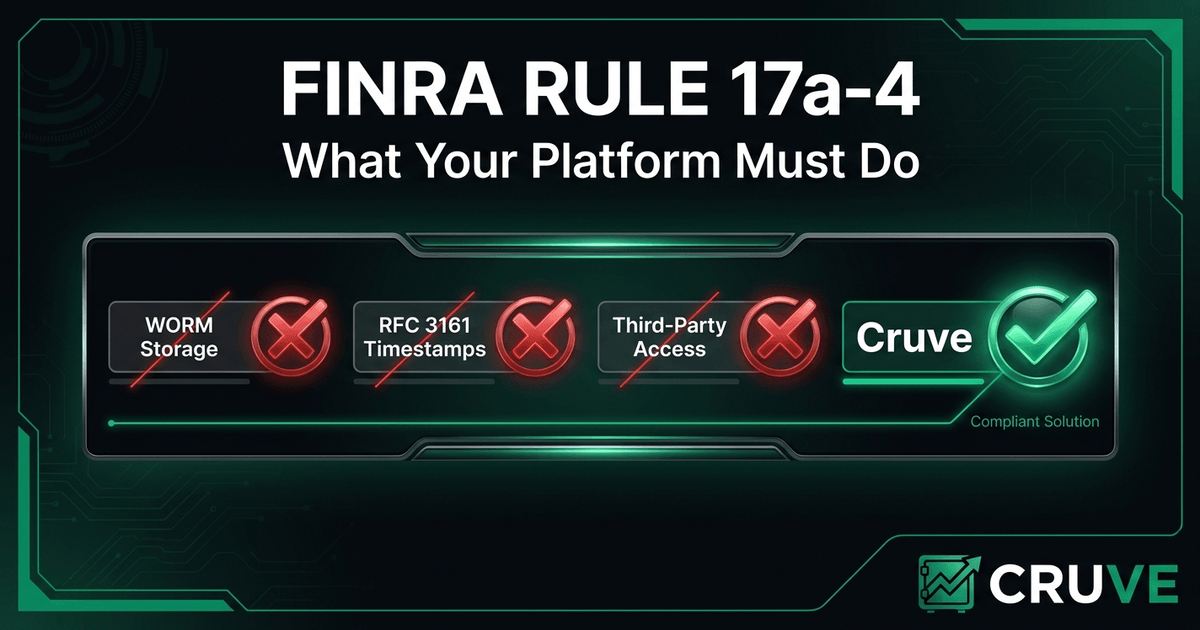
When FINRA examiners review a firm's communications archiving system, they typically probe:
- Can the firm demonstrate that all electronic business communications are captured, regardless of platform?
- Is the archive storage system genuinely WORM-compliant, or does it have administrative override capabilities?
- Are timestamps cryptographically verifiable, or are they application-level records that could have been modified?
- Is there an independent third party with the technical ability to download the complete archive?
- How quickly can specific records be retrieved in response to an examiner's request?
Firms that can answer these questions with technical specificity demonstrate a compliance posture that survives examination. Firms that answer with "we have an archiving system" invite deeper scrutiny.
READY TO BUILD A COMPLIANT COMMUNICATIONS PROGRAM?
Cruve is purpose-built for FINRA and SEC-regulated firms — E2EE, WORM archiving, and supervisory review in one platform.
Request Early Access